This article was written by Werner Wermak.
Content
- Social engineering and phishing
- Refer to the poisoning scam
- Divide and make excuses
- Malicious browser extension
- Fake Airdrops and Giveaway Scams
- Scams and Deepfakes with AI enabled
- Romance Scam “Pig Extortion”
- Fear and panic tactics
- Breakup plans
- Developer intent and supply chain risk
As Web3 usage expands in 2026, security risks will increase in complexity and scope. The threat landscape now extends far beyond simple fraud to include advanced AI-powered attacks and highly targeted campaigns that exploit human behavior and system flaws.
According to comprehensive information 2026 guide to crypto security threats from Kerberus, a true Web3 security browser extension, Web3 ecosystems face a wide range of digital threats that can include wallets, smart contracts, private keysand even the developers themselves.
Understanding the most common risks facing Web3 users and developers today is critical to protecting digital assets.
Below, we outline the top 10 Web3 security threats shaping 2026 and explain how users can stay safe with CoolWallet.

1. Social engineering and phishing

Social engineering remains a pervasive threat on the Web3, exploiting human psychology rather than technical vulnerabilities. Phishing attacks have evolved into sophisticated operations where attackers impersonate trusted platforms and trick users into sharing sensitive information or signing malicious transactions. These schemes now include cloned decentralized applications, fake social media support channels, and scams delivered through highly tailored messages via email and messaging apps.
2. Refer to poisoning scams
Address poisoning is a deceptive technique where attackers send small, seemingly innocuous transactions from fake wallet addresses that look like legitimate addresses. Later, users who copy addresses from recent activity may mistakenly send assets to wallets controlled by the attacker, causing irreversible losses.

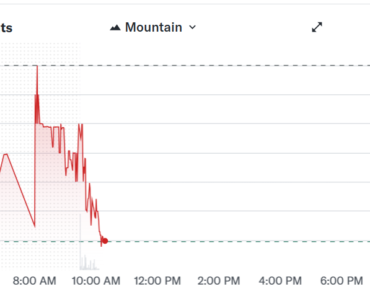
Source: Chainalysis
Just recently, a poor investor lost $50 million when he sent crypto to the wrong address.
3. Divide and make excuses

Attackers are increasingly using spoofing tactics, posing as customer support or project administrators to extract seed phrases, private keys, or transaction confirmations. Impersonators often use social media and fake channels to increase urgency and make victims likely to follow without investigation.
4. Malicious browser extension

Fake browser extensions that purport to offer security enhancements or wallet utilities often contain malicious code designed to steal credentials or private keys. Once installed, these extensions can act as wallet drains or telemetry collectors, providing constant access to attackers.
5. Fake Airdrops and Giveaway Scams
Fraudsters use “free token” incentives to lure users into linking their wallets to dubious intellectual contracts. These contracts may be legitimate, but are designed to drain assets after the wallet is authorized. Some campaigns use AI to generate persuasive advertising content or celebrity endorsements.
6. Scams and Deepfakes
In 2026, artificial intelligence (AI) tools have become double-edged swords. They are now used to create highly convincing phishing messages, automated fraud agents and deepfake content that can mimic real people or brands with alarming fidelity. AI agents often adapt their tactics in real-time based on user responses.
7. Fraud in romance “Pig Butcher”
This emotional manipulation scam involves attackers building up their victims for weeks or months before introducing fraudulent investment opportunities, exploiting the affections of their victims to extract funds. After transferring funds, withdrawals fail or accounts disappear.
8. Tactics of fear and panic
Scareware exploits fear of loss by providing false alerts about wallet compromise or malware infection. These fraudulent alerts often direct users to dubious sites where attackers collect credentials or push the installation of malware.

Source: Kaspersky
9. Arrest Plans
Phishing attacks exploit human responses to perceived opportunity by offering rewards, bonuses, or exclusive benefits that induce victims to divulge private information or sign risky transactions.

Source: Kaspersky
10. Developer Objective and Supply Chain Risk
Hackers no longer limit their targets to everyday users. Complete teams now focus on developers and Web3 infrastructure, realizing that a single code base or developer workstation can expose entire platforms or protocols. Recent reports highlight AI-generated malware campaigns targeting blockchain developers and highlight the extent of the attack beyond just user wallets.
Why these threats matter in 2026
Web3’s decentralized design offers users unprecedented control over digital assets, but eliminates centralized security networks. Unlike traditional banking, blockchain transactions are irreversible once confirmed. Once a seed phraseprivate key or transaction confirmation is compromised, recovery becomes virtually impossible. Real-world data underscores these risks: Web3 theft continues, and billions of dollars have been lost to hackers and fraud in recent years.
Human errors and behavioral vulnerabilities remain a major factor in losses, as traditional security tools often fail to address real-time threats or social engineering tactics. According to Kerberus’ analysis, only a fraction of existing Web3 security tools offer real-time user protection, leaving many users vulnerable even with basic precautions.
How CoolWallet navigates emerging risks

Battle-tested hardware wallets like CoolWallet (crypto user protection since 2014) plays an important role in protecting digital assets by isolating key signatures from potential software environments.
Here’s why:
- Unlike software wallets, hardware wallets store private keys offline.
- This massively reduces your exposure to online threats such as phishing, malicious extensions, and malware.
- Even when attackers trick users into connecting to malicious sites, their private keys are stored inside the device’s hardware and are never exposed in a vulnerable browser environment.
Private key isolation
CoolWallet stores crypto private keys in an EAL6+ secure element inside the device. This means that even if a connected computer or mobile device is compromised, the private keys used to sign transactions never leave the hardware.

This protects against keystrokes, buffer hijacking and similar threats that target key content. Hardware isolation dramatically reduces the attack surface for many of the listed threats where credential theft is the primary goal.
Transaction verification
In addition to key separation, CoolWallet allows out-of-band transactions to be verified. Before completing any transaction, users can review and confirm details directly in the hardware wallet itself, ensuring that they are not unknowingly approving malicious contracts or unauthorized transfers caused by phishing sites or fake DApps.
Multi-layer protection
CoolWallet provides additional layers of security such as Encrypted Bluetooth communication, and support for multi-signature workflows. These features push against unauthorized access and make automated attacks more difficult. Multiple layers of authentication mean that even the most sophisticated social engineering campaigns struggle to get past defenses without the user’s explicit consent on the device.
CoolWallet’s built-in Web3 browser also enjoys integrated support through Blockaid’s security tool.
User education and awareness
Security tools are effective, but user behavior remains a major vulnerability. CoolWallet complements hardware protection with clear guidance on best practices that emphasize treating URLs with care, avoiding copying addresses from unverified sources, and maintaining solid operational security habits. In a landscape where fraudsters are rapidly adapting to AI, user education is an important frontline defense.
CoolWallet Range: Go or Pro?

CoolWallet Pro
CoolWallet Pro is a hardware wallet designed for crypto users who want strong security when using DeFi, NFTs and multiple blockchains. It stores private keys inside a secure CC EAL6+ certified chip, so sensitive data never leaves the device or is exposed to malware, phishing sites or infected computers.
The wallet connects to your phone via encrypted Bluetooth, but only signed transaction data is shared. Before any transfer can take place, you must verify it on a physical device using a PIN or biometric security. This extra step helps stop unauthorized transactions caused by fake websites or malicious DApps.
CoolWallet Pro also supports staking, token swaps and WalletConnect access to decentralized applications. This means users can interact with Web3 services while keeping funds in cold storage, reducing the risk of wallet drains, credential theft, and other common attack methods.
CoolWallet Go
CoolWallet Go extends CoolWallet’s hardware security approach with a simplified cold storage device designed for everyday Web3 use. The card-style wallet generates and stores private keys inside a CC EAL6+ certified secure element that keeps sensitive key material completely offline and from malicious access, phishing sites or compromised browsers.
Instead of relying on cables or permanent wireless connections, CoolWallet uses Go. NFC communicationwhich reduces exposure to remote attack vectors while allowing appropriate transactions to be authorized by the companion application.
A major security improvement is its wireless backup card system, which eliminates the need to type recovery phrases that are often used in social engineering and impersonation fraud.
By combining offline key separation, secure transaction verification and secure recovery methods, CoolWallet Go helps users interact with DeFi, NFTs and DApps while reducing the risk of wallet drains and credential theft.
Conclusion
The Web3 security landscape in 2026 will see sophisticated threats that mix psychological manipulation, technical exploits and AI automation. Using CoolWallet’s hardware wallet and application protection, as well as real-time Web3 transaction monitoring, users can protect their digital assets in highly risky environments.