China Internet Finance Association Risk Alert: OpenClaw Security Risks Explained
The China Internet Finance Association has issued a warning about the security of the OpenClaw program. The warning puts OpenClaw’s security risks in the spotlight, highlighting concerns related to financial stability, data protection, and operational stability.
A review of regulatory notices and security studies reveals recurring risk themes: unsafe default configurations, extended autonomy, and exposure to third-party expertise. These factors can increase the consequences if OpenClaw is deployed without enterprise-level controls or management.
Why it matters to businesses and regulated industries
According to the Ministry of Industry and Information Technology, secure deployments, especially those that remain in default, require stronger authentication, stricter access controls and auditing of public network exposure. This meets the expectations of internal controls in financial services, government and critical infrastructure.
The National Computer Network’s Emergency Response Technical Team noted the potential for system crashes, data leaks, or misuse if OpenClaw is adopted without sufficient safeguards. For regulated entities, which raises issues related to liability, audit and duty of care.
Permission misconfiguration is a primary risk, as OpenClaw can chain skills and increase risk if even one component is untrusted or malicious. Exposed defaults, credentials, network access, or permission policies can similarly expand the blast radius.
Autonomy can trump control if actions are initiated by a machine with minimal human input, increasing the possibility of unexpected changes to systems or data. According to Colin Shea-Blimer of Georgetown CSET, small configuration errors can increase when agents configure powerful capabilities in tools.
Experts have warned that the general design, broad permissions and autonomy, can allow unexpected damage in the absence of strong shelters. Gary Markus, an AI researcher, said “disaster awaits,” describing the danger if autonomous agents operate with insufficient oversight.
Sizes and versions for a more secure OpenClaw deployment
According to a disclosure by Oasis Security, a critical chain of vulnerabilities allowed websites to silently control an OpenClaw agent through a web interface; installation is recommended to update to version 2026.2.25 or later. Version control should be coupled with change management, rollbacks, and environmental isolation.
Risk mitigation also depends on layered controls: identity and access management, network segmentation, data loss prevention, logging and authentication of people during operations for sensitive or irreversible actions. These measures help balance autonomy with corporate responsibility.
Enterprise Hardness Checklist: Authentication, Access Control, Audits, and Independence Limits
- Implement strong authentication (MIA, SSO) and least privilege role design.
- Change defaults; turn secret; disable unused skills and dangerous abilities.
- Network output limitation; segment execution time; Use permission lists for domains and skills.
- Require people’s permission to perform hazardous tasks; determine autonomy and spending limits.
- centralization of accounting; enable audit trails; review permissions weekly.
- Veterinary qualifications of third parties; pin versions; code and perform a quick injection test.
- Implement WAF/proxy control; data leakage monitoring; simulating the opposite use.
- Keep backup plans; stage update; check the integrity of the product before release.
Research Summary: Cisco Findings and Oasis Security Update Guide
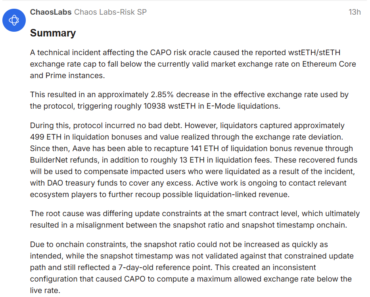
The AI threat and security research team described Cisco OpenClaw as very dangerous when configured incorrectly and reported nine issues, including two critical issues in the ClawHub skill, with data exfiltration and rapid switching between findings.
Oasis Security disclosed a plugin-free way through the web interface and recommended updating to 2026.2.25+. Together, these reports highlight that the security posture depends on both upstream and downstream configuration of the enterprise.
Questions about OpenClaw security risks
What specific vulnerabilities have researchers found in OpenClaw and its skill catalog?
Reported problems include injection, data exfiltration, nine flaws (two critical) in the public skill and the web interface capture chain, which are fixed in version 2026.2.25+.
What do Chinese regulators (CIFA, MIIT, CNCERT) advise on OpenClaw deployment?
They warned of the risk and called for stronger approvals, tighter access controls, public impact audits and more awareness for finance and critical infrastructure.
| DISCLAIMER: The information on this website is provided as a general overview of the market and does not constitute investment advice. We encourage you to do your own research before investing. |