Prefer us on Google
A recently published paper by Ark Invest and crypto financial services company Uchained argues that more than two-thirds of the total BTC supply is already immune to quantum attacks. Due to the rapid growth of the quantum sector and its perceived ability to subvert BTC’s SHA-256 algorithm, the nefarious threat is back in the debate among crypto users and development circles.
However, an extensive study by ARK Invest and Unchained proves that the lion’s share of the entire supply (65%) has already been proven to be quantum, and there is enough time left to improve the system to provide the remaining amount (34.6%) from the next generation of computing.
Eliminate the quantum threat
The article defines five stages of quantum effects:
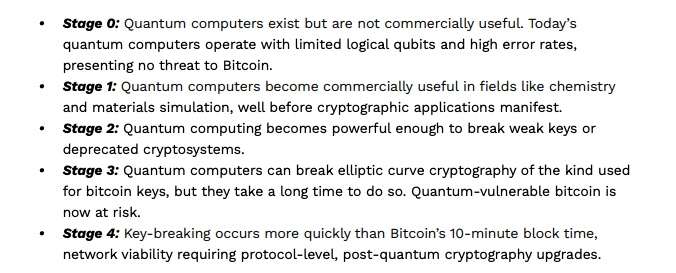
Currently, the quantum threat remains between Stages 0 and 1, indicating that it is too early to cause mass panic in the digital currency economy. The transition to quantum computing involves several intermediate levels of awareness and turning points, giving developers plenty of time to introduce the necessary updates.
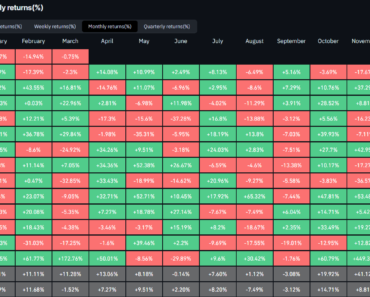
The document also breaks down Bitcoin’s supply chain and its vulnerability to incoming quantum computing threats:
 
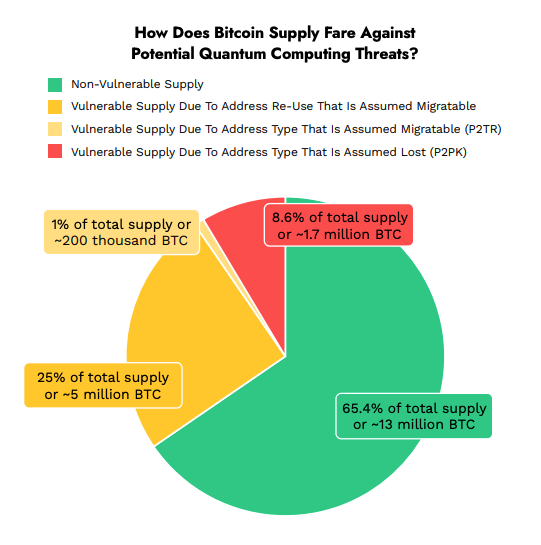
These groups include:
- The first P2PK (Pay-to-Public-Key) addresses (8.6%) of the total supply where the public key is visible. They are the most vulnerable.
- Address Reuse (~5M BTC): This is another vulnerable area, but can be addressed over time. This is when the address sends and receives BTC; The public key will be visible.
- P2TR Addresses (Taproot) (~200k BTC): The white paper indicates that the current root implementation where the address is transferable can be used.
- Secure provision (65.4%): Most modern Bitcoin addresses (P2PKH, P2SH and P2WPKH) only reveal a public key hash. A quantum computer, despite its enormous advantages, cannot derive a public key from its own hash.
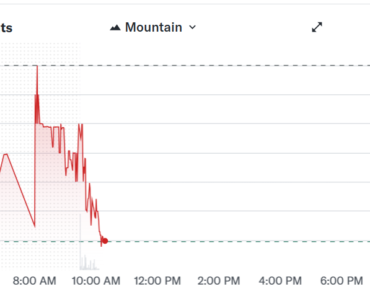
The aging chart shows that most of the supply is already immune to quantum threats or can be protected with the necessary upgrades. The issue of BTC in the P2PK era is a more difficult part of the puzzle that requires further consideration by developers.
The future
Although quantum computing does not pose an imminent threat to a significant portion of the BTC supply, the network should adopt quantum-safe protocols to increase user trust and ensure long-term stability.
The new update, BIP 3160, is already addressing quantum network resistance, but it’s likely only a temporary fix in the grand scheme of things.
Prefer us on Google