Crypto hackers who tried to use “ClickFix” attacks to steal crypto have now resorted to impersonating venture capital firms and hijacking browser extensions in their latest two attacks.
Scammers are using fake venture capital firms like SolidBit, MegaBit and Lumax Capital, according to a report from cybersecurity firm Moonlock Lab on Monday. Hackers use companies to contact users through LinkedIn with affiliate offers and then redirect them to fake Zoom and Google Meet links.
When a target clicks on the fraudulent link, they are taken to an event page with a fake Cloudflare “I’m not a robot” checkbox. Clicking on it copies the malicious command to the clipboard and prompts the user to open a terminal on their computer and enter a so-called verification code that executes the attack.
“The ClickFix technique is what makes the final step so effective,” said the Moonlock Lab team. “By turning the victim into an execution mechanism – hooking them up and executing commands – attackers bypass the controls the security industry has built for years. No exploits. No suspicious downloads.”
Moonlock Lab alleges that an individual using the name Mykhailo Hureyev, listed as co-founder and managing partner of SolidBit Capital, was the primary point of contact for the initial stage of the LinkedIn scam. Two X users also reported suspicious conversations with Hureyev’s account.

However, Moonlock Lab notes that the campaign’s infrastructure is complex and designed to change identities when a front is exposed.
Chrome extension hacked to steal crypto
Meanwhile, crypto hackers have been distributing a suspicious Chrome extension with the “ClickFix” attack angle until recently.
John Tuckner, founder of cybersecurity firm Annex Security, said in a February 23 report that QuickLens, an extension that allows users to run Google Lens searches directly in their browser, has been removed from the Web Store after it posed a risk of spreading malware.
After QuickLens changed ownership on February 1, a new version was released two weeks later that contained malicious scripts that launched ClickFix attacks and other data-stealing tools. Tuckner noted that the extension has about 7,000 users.

The hijacked extension reportedly searched for crypto wallet information and seed phrases to steal funds. According to a report by eSecurity Planet on March 2, it also scraped the contents of Gmail inboxes, YouTube channel information and other login credentials or payment information entered into web forms.
ClickFix attacks are used to target many industries
According to Moonlock Lab, the ClickFix technique has gained popularity among threat actors since last year because it forces victims to manually execute the payload, bypassing standard security tools.
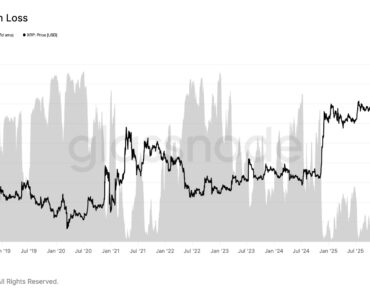
related to: Crypto losses in February hit their lowest level since March 2025, PeckShield says
However, security researchers have been tracking its use since at least 2024, with targets spanning a wide range of industries.
Microsoft Threat Intelligence warned last August that it was tracking “daily attacks against thousands of enterprise and end-user devices worldwide.”
Meanwhile, cyber threat intelligence firm Unit42 reported last July that “relatively new social engineering techniques” are affecting industries such as manufacturing, wholesale and retail, state and local government, utilities and energy.
Magazine: Would Bitcoin Really Be $200K If Not For Jane Street? Trade secret