U.S. and European authorities said Thursday they have disrupted SocksEscort, a dubious proxy service used by cybercriminals to hide their identities during fraud, including the hijacking of cryptocurrency accounts.
The DOJ said the service compromised at least 369,000 routers and other Internet-connected devices in 163 countries, giving cybercriminals control over proxies that hid their real IP addresses.
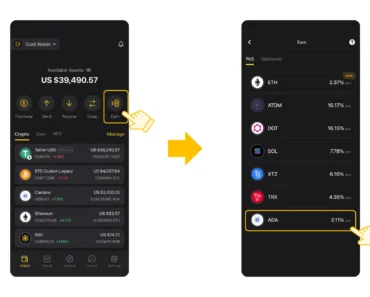
The platform has reportedly enabled crimes including bank fraud and the hijacking of cryptocurrency accounts since 2020. In one case cited by prosecutors, a victim in New York lost nearly $1 million worth of crypto-assets.
Officials said they seized 34 domains, crashed about two dozen servers in seven countries and froze about $3.5 million in cryptocurrency linked to the operation.
The network received at least $5.7 million from users
According to Europol’s statement, customers used a payment platform to access the proxy service, which allowed them to buy it anonymously with cryptocurrency.
Investigators estimate that SocksEscort took at least 5 million euros ($5.7 million) from its users.
Europol Executive Director Catherine De Bolle said: “Proxy services like ‘SocksEscort’ give criminals the digital cover they need to launch attacks, distribute illegal content and evade detection.”

“Operations like this show that when investigators connect the dots internationally, the infrastructure behind cybercrime can be exposed and shut down,” he said.
Various institutions of the country participated in this operation
The takedown was part of a coordinated international effort involving law enforcement agencies from Austria, France, the Netherlands, Germany, Hungary, Romania and the US.
The FBI Sacramento Field Office, the Department of Defense Criminal Investigation Service of the Inspector General, and the IRS Oakland Office of Criminal Investigation were among the U.S. agencies. Europol and Eurojust provided investigative and operational support for cross-border operations.
related to: A Swedish investigation reported the leak of the source code of an e-government platform
The DOJ also acknowledged the assistance of Black Lotus Labs, the threat intelligence unit of U.S. telecommunications company Lumen Technologies, and the nonprofit Shadowserver Foundation, which provided technical information during the investigation.
According to The Hacker News, SocksEscort relied on malware called AVrecon, the details of which were publicly documented by Black Lotus Labs in July 2023.
Magazine: All 21 million bitcoins from quantum computers are at risk